Jammin’ with James Recapped: Zero Trust with Microsoft Services, Data Protection and Threat Intelligence

This continues our series about implementing Zero Trust with Microsoft Services. If you missed our post about device trust and security, you can check it out now. This guide will show you how to use sensitivity labels and threat intelligence to protect your Microsoft environment from cyber-attacks.
Labels:
Sensitivity labels are an essential aspect of Zero Trust Security and allow you to determine who can access specific data at certain times. To create a label, go to the information protection tab at Microsoft Purview (purview.microsoft.com).
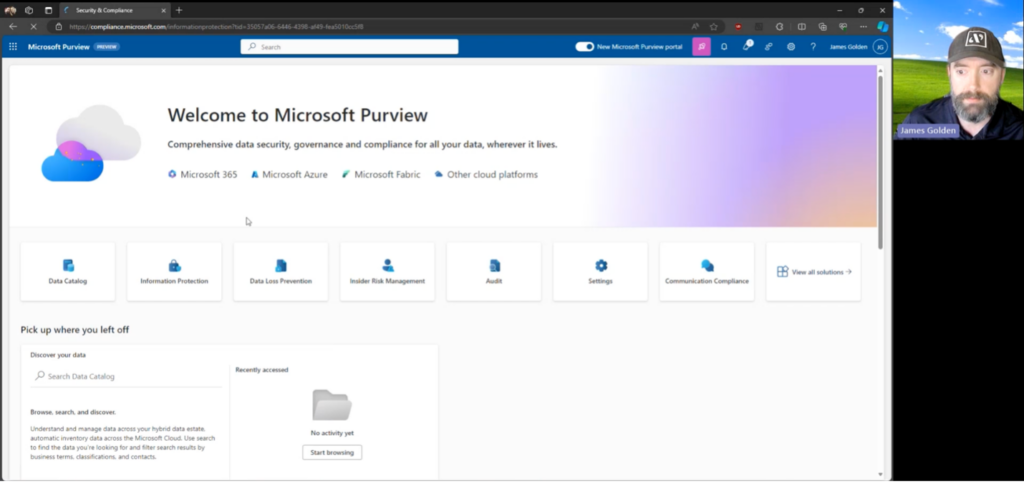
On the overview tab of that page, you can create new labels and choose which applications they are applied to. Microsoft is highly customizable, allowing you to specify the priority and scope of the label.
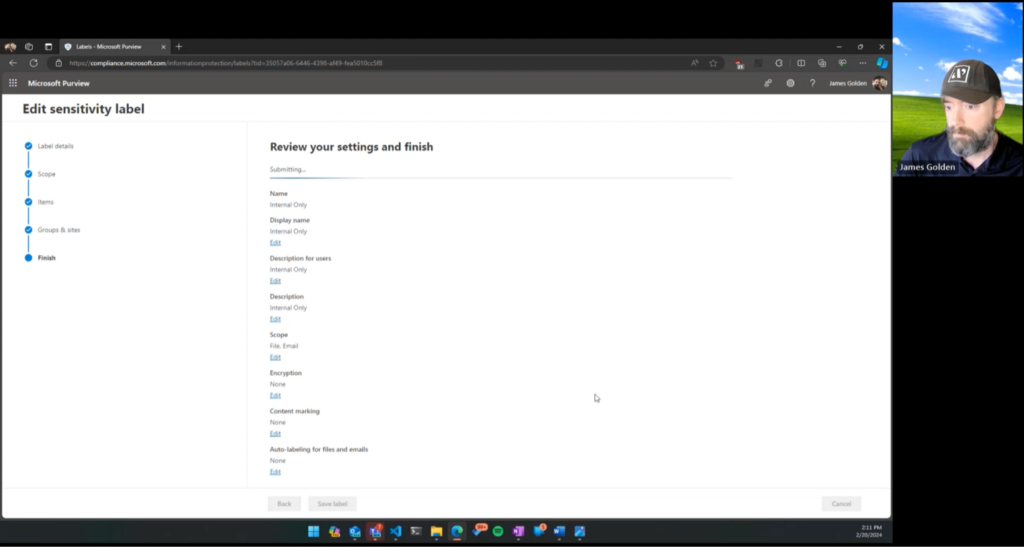
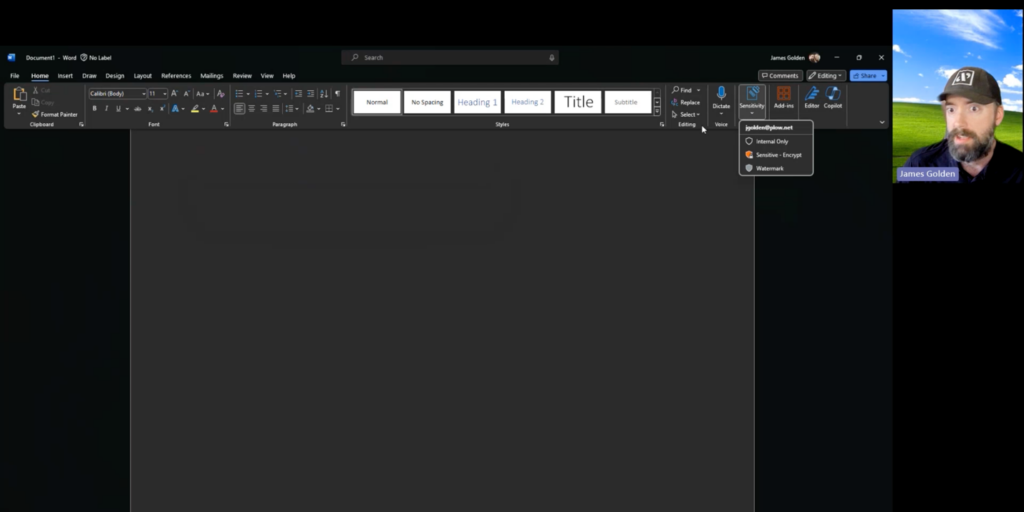
After saving your label, you can create a label policy, which controls what users have access to that label. This feature also allows you to create settings that force users to justify removing a label or lowering its classification. Your labels should appear on your Microsoft apps about 24 hours after creation. For example, here you can see sensitivity labels as they appear on Microsoft Word:
Under the information protection tab, you can also create retention labels, which are made to replace retention policies. These can be created for activities like qualifying how long an email should be kept in a specific inbox.
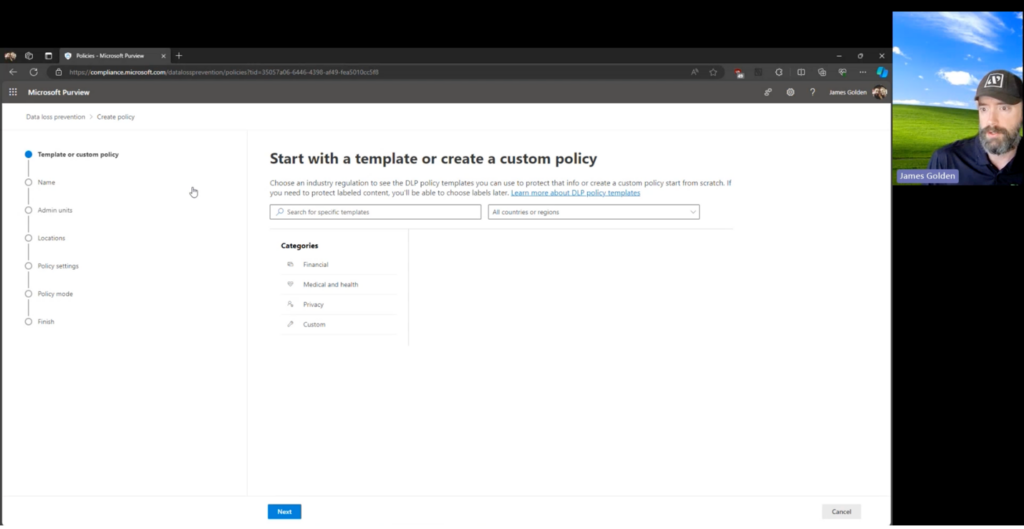
Data Loss Prevention labels are another recommended step for your company to improve its cybersecurity practices. These labels tell you that if someone is trying to send data somewhere, it should not go. To create these labels, navigate to the Solutions tab of Microsoft Purview. Go to the Policies section of the Data Loss Prevention page from here. Microsoft has some templates to create new labels, or you can create your own. Here, you can add admin units, choose where the label is applied, and create custom rules for your policy.
Threat Intelligence:
Another step to move your company towards Zero Trust is intelligence alerting. To implement this, navigate to Microsoft Defender (security.microsoft.com).
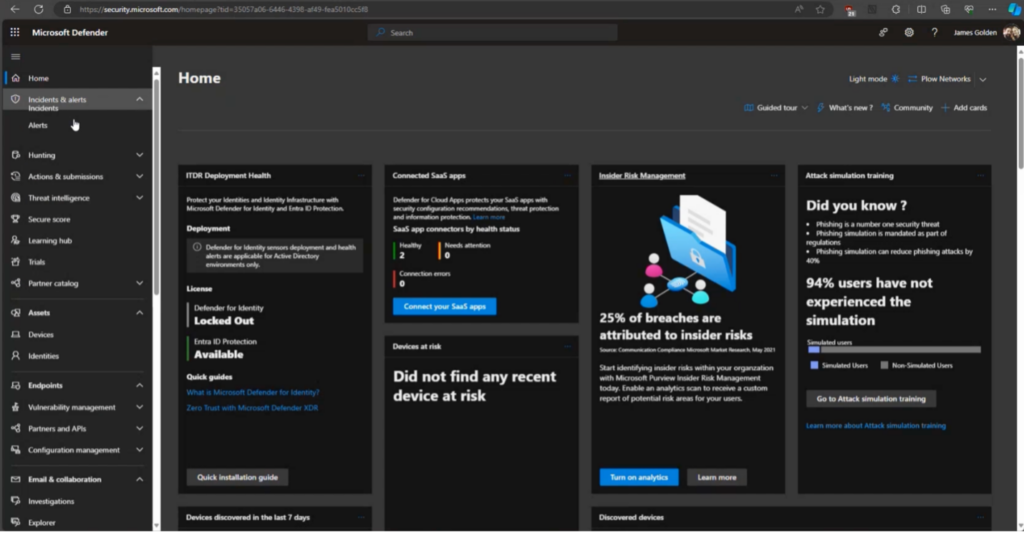
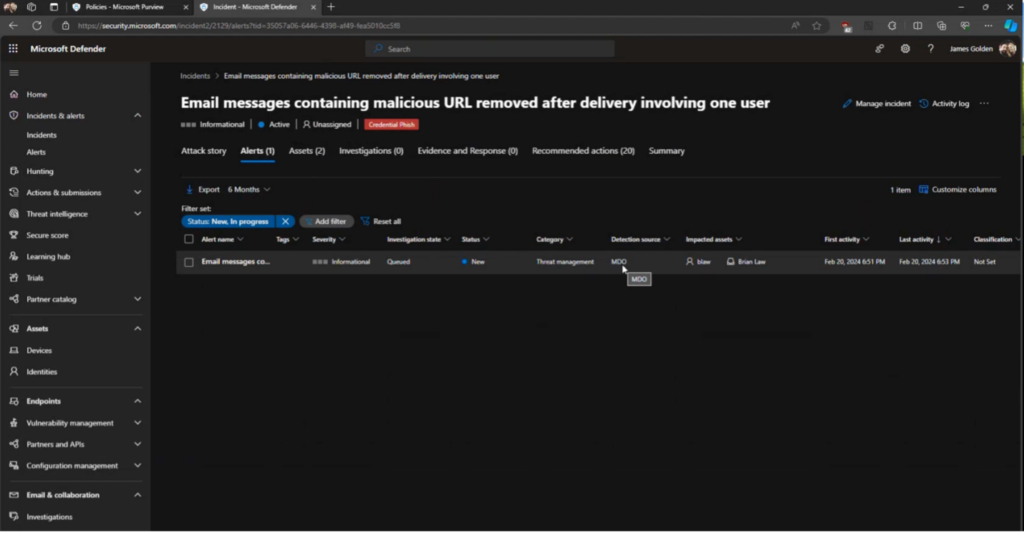
This program allows you to monitor both incidents and alerts. Alerts are single events, such as an unauthorized user logging in to your environment. Incidents are collections of alerts that form into a timeline. Clicking on an incident will show you threat levels for different alerts and a full summary with granular details, such as what time the threat occurred. To pinpoint the source of an alert, navigate to that alert on the incidents page.
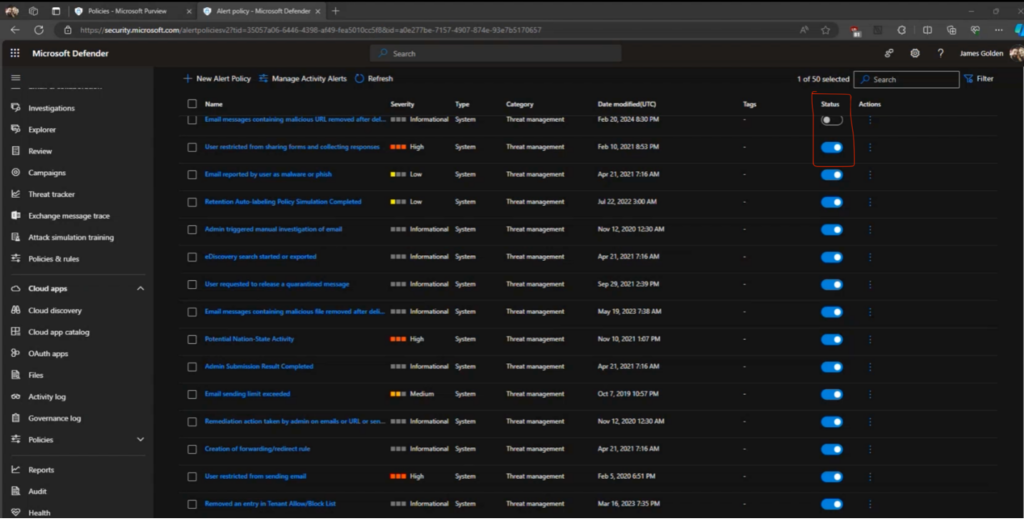
This section also allows you to change which alerts you receive notifications for. Click on the Email & Collaboration tab, navigate to the Policies & Rules page, and then find the Alert Policy section. Each alert will have its specific information set, but to turn notifications on or off, click the bar underneath the “Status” header for whichever policy you want to start or stop receiving alerts for.
You can create rules on the main Microsoft Defender page that supersede all other alert policies. Navigate to Settings, click on Microsoft Defender XDR, go to the Rules section, and click Alert Tuning. Here, you can set the alert properties that you want to implement.
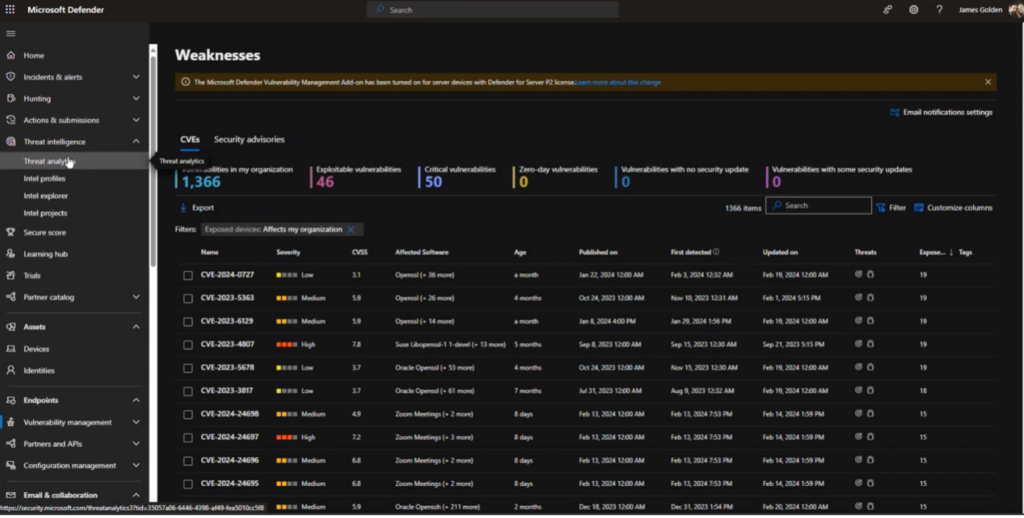
Lastly, you should check your threat analytics to see which endpoints are exposed to threats and how vulnerable they are. To do this, explore the Threat Intelligence tab’s Threat Analytics page on Microsoft Defender.
By following this guide, you can implement safer practices that protect your company from breaches or cyber-attacks. Register here for our next’ Jammin’ with James’ webinar on March 20, 2024, to learn more about Zero Trust with Microsoft Services and how your organization can optimize your Microsoft licensing.
Explore more on: