Endpoint Management Solutions for Mid-Sized Businesses

Imagine this scenario: While conducting a routine security audit, your IT director discovers that 30% of company devices have not been patched in the last 60 days. An unpatched environment increases business risk and creates unnecessary costs, such as regulatory fines, data breach recoveries, and productivity losses from unmanaged endpoints.
This scenario is a reality that many businesses with poorly managed endpoints have faced and will continue to face. As organizations adapt to the realities of a distributed workforce post-2020, they must implement stronger solutions that ensure endpoint protection. IT leaders face mounting pressure to secure and manage endpoints across remote offices, home networks, and mobile devices, all while balancing compliance and efficiency.
In this article, we will share a practical evaluation framework, a step-by-step implementation roadmap, and insights for comparing leading endpoint management solutions. Whether you’re in healthcare, finance, or logistics, you will find actionable strategies to reduce risk and improve operational outcomes for your business.
Why Traditional IT Management Fails at Scale
For many mid-sized businesses, manual IT processes become unsustainable around the 100-device threshold. Processes such as creating spreadsheets, running remote desktop sessions, and patching individual devices begin to overload internal teams. IT staff find themselves chasing tickets instead of innovating their strategy to improve operational efficiency.
Employees often turn to shadow IT to bypass slow, manual processes and complete their work more quickly. This results in a fragmented environment where visibility vanishes, and risk multiplies. Compliance documentation for regulatory acts like HIPAA and SOX turns into a nightmare, with endpoints slipping through the cracks and audit trails missing key data.
Each unmanaged endpoint can cost up to 3x more in support time, draining resources and delaying resolution. In a 150+ device environment, the difference between manual and automated endpoint management is both operational and financial. Automated systems reduce repetitive tasks, freeing up IT teams to focus on strategic initiatives that advance business progress.
Consider the case of a regional healthcare practice that failed a HIPAA audit due to unmanaged endpoints. The fallout included regulatory penalties, reputational damage, and a costly overhaul of their IT infrastructure. It’s a cautionary tale that underscores the urgency of modernizing endpoint management before scale becomes a liability.
Core Components of Modern Endpoint Management Solutions
Modern endpoint management is about delivering real-time visibility, automated control, and seamless integration across a diverse ecosystem. For IT leaders managing 100 or more devices, quarterly audits and manual patching are no longer sufficient.
Instead of relying on outdated inventory tracking, modern solutions provide real-time device inventory, giving IT teams instant insight into which endpoints are connected, where they are located, and how they are configured. This visibility is critical for proactive security and compliance.
Automated patch management is another key feature of modern endpoint management solutions. It is designed to deploy updates outside of business hours, minimizing user disruption and maximizing productivity. Automation effectively eliminates the chaos of Patch Tuesday, which derails operations and leaves users frustrated.
While security policies must be enforced, this should not come at the expense of usability. The best endpoint management tools strike a balance, applying policy enforcement that is both firm and flexible. Cross-platform consistency is another non-negotiable. Whether your business uses Windows, macOS, iOS, or Android, a Unified Endpoint Management (UEM) solution brings all devices under one umbrella, eliminating gaps and reducing complexity.
For organizations with existing Microsoft infrastructure, integration matters. Modern tools should integrate with existing Microsoft environments, leveraging Intune, Azure AD, and Defender to streamline workflows and enhance security posture.
Unified Endpoint Management (UEM) Architecture
Software redundancy can create security gaps that increase the risk of unauthorized access to your digital environment. Each tool may serve a purpose, but without centralized coordination, gaps emerge between patching, access control, and compliance enforcement. Similarly, integration failures between endpoint and identity management systems can lead to misaligned policies and an inconsistent user experience. These breakdowns frustrate IT teams and expose your business to regulatory and operational threats.
That’s why Unified Endpoint Management (UEM) should be a key part of your endpoint management strategy. By consolidating devices, applications, and identities into a single architecture, UEM eliminates silos, streamlines workflows, and strengthens security posture.
The Evolution of Endpoint Management
The journey from Mobile Device Management (MDM) to Enterprise Mobility Management (EMM) to today’s UEM reflects the growing complexity of modern IT environments. UEM enables centralized control across Windows, macOS, iOS, Android, and even IoT endpoints.
Now, with the rise of modern management, cloud-native platforms are replacing legacy infrastructure, offering real-time visibility, automation, and policy enforcement without the overhead of on-prem servers.
Microsoft Intune: The Cornerstone for Microsoft 365 Environments
For organizations that already implement Microsoft 365 products and services, Microsoft Intune often becomes the logical foundation for UEM. It integrates seamlessly with Azure AD, Defender for Endpoint, and Microsoft Purview, enabling policy-based management and conditional access across the enterprise.
What Approach Works Best for Mid-Sized Companies?
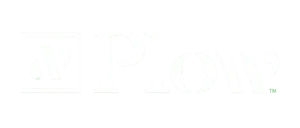
Mid-sized businesses face a critical decision: build a custom UEM stack, buy a turnkey solution, or adopt a hybrid approach. Each path has trade-offs:
Migrating Without Disruption
Transitioning from legacy tools doesn’t have to mean downtime. A phased migration strategy can minimize disruption while allowing IT teams to validate policies and workflows in real-world conditions.
Selecting Endpoint Management Solutions for Your Industry
Endpoint management isn’t a one-size-fits-all approach, especially when compliance, device diversity, and operational environments vary dramatically across industries. Choosing the right solution means aligning technical capabilities with regulatory demands and business needs.
Healthcare: In healthcare, endpoint management must support HIPAA compliance, medical device isolation, and Protected Health Information (PHI) requirements. Solutions should offer granular access controls, encrypted data flows, and audit-ready reporting to avoid costly violations and ensure patient trust.
Financial Services: For financial institutions, SOX compliance, transaction security, and audit trail integrity are non-negotiable. Endpoint tools must integrate tightly with identity management systems and provide real-time visibility into device activity to support internal and external audits.
Manufacturing & Logistics: In manufacturing and logistics, the convergence of Operational Technology (OT) and Information Technology (IT) introduces new challenges. Solutions must support ruggedized devices, secure supply chain endpoints, and maintain uptime in harsh environments. Cross-platform support and remote monitoring are essential for distributed operations.
Regional Considerations: Businesses in Tennessee and the broader Southeast often face unique regulatory requirements and infrastructure constraints. Selecting a vendor with regional expertise and familiarity with state-level compliance nuances can streamline implementation and reduce risk.
Implementation Roadmap for Endpoint Management
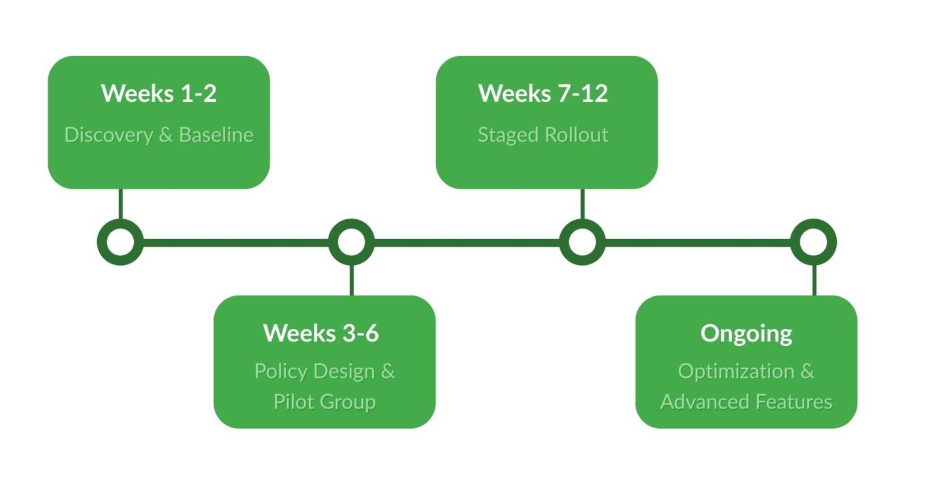
Deploying a modern endpoint management solution requires a structured rollout, stakeholder alignment, and a realistic timeline. Rushing implementation often leads to failure, especially when users feel blindsided by new controls or perceive monitoring as surveillance. Here is a four-phase roadmap designed to help mid-sized organizations develop an endpoint management strategy.
Phase 1: Discovery and Baseline (Weeks 1—2)
Begin by recording a full inventory of existing endpoints, configurations, and vulnerabilities. Establish a baseline for patch status, compliance gaps, and device diversity. This phase sets the foundation for policy design and prioritization.
Phase 2: Policy Design and Pilot Group (Weeks 3—6)
Develop endpoint policies tailored to business needs, ensuring they balance security with usability. Select a pilot group from a low-risk department to test patching schedules, access controls, and user experience. Gather feedback and refine policies before rolling your plan out to all employees.
Phase 3: Staged Rollout by Department/Risk Level (Weeks 7—12)
Deploy endpoint management tools in phases, starting with high-risk departments, such as finance. Use automated workflows to enforce policies and monitor compliance. Maintain open communication with department leads to address concerns and ensure adoption.
Phase 4: Optimization and Advanced Features (Ongoing)
Once core functionality is stable, introduce advanced features like automated threat response, remote wipe, and integration with identity platforms. Continue refining policies based on usage data and evolving business needs.
Change Management: Securing User Buy-In
Successful implementation hinges on stakeholder engagement. Develop a clear communication plan that explains the business value to executives and reassures users about privacy protections. Transparency and training go a long way in reducing resistance.
Measuring Success and ROI
To track the progress of endpoint management initiatives, they must be tied to measurable outcomes. Security, operations, compliance, and financial performance are all critical, but the key to effective endpoint monitoring is translating technical wins into executive-friendly metrics.
Security Metrics: Track mean time to patch and vulnerability exposure windows to demonstrate how quickly threats are mitigated. These metrics show how endpoint management directly reduces risk and strengthens the organization’s security posture.
Operational Metrics: Monitor ticket volume reduction and first-call resolution rates to quantify efficiency gains. Fewer help desk escalations and faster resolutions mean IT teams can shift focus from firefighting to strategic initiatives.
Compliance Metrics: Measure audit pass rates and documentation completeness to validate regulatory alignment. Whether it’s HIPAA, SOX, or state-level mandates, strong endpoint controls simplify compliance and reduce audit fatigue.
Financial Metrics: Highlight license optimization and hardware lifecycle extension to show cost savings. By reclaiming unused licenses and extending device usability through proactive management, IT leaders can make a compelling case for ROI.
Tools like KPI dashboards will help your organization visualize key metrics to track the performance of your endpoint management system. This is especially important in establishing visibility and support with executive leaders.
Endpoint Management FAQs
- What is an endpoint management solution? An endpoint management solution is a comprehensive platform that helps IT teams secure, configure, and monitor endpoints across the organization. For growing businesses, it plays a critical role in maintaining compliance, reducing operational overhead, and improving visibility across desktops, laptops, mobile devices, and more.
- How does endpoint management differ from endpoint security? While endpoint security focuses on protecting devices from threats (e.g., malware, unauthorized access), endpoint management encompasses a broader scope. It includes operational control, policy enforcement, patch automation, lifecycle management, and integration with identity systems. In short, endpoint management includes security, but it also ensures devices are configured, compliant, and optimized for performance.
- What is the typical cost of endpoint management solutions for 100—200 users? Total cost of ownership (TCO) typically includes licensing fees, implementation services, and ongoing management overhead. For mid-sized organizations, expect a range of $40-$70 per device/year, depending on feature depth, support level, and deployment model. Implementation costs may vary based on complexity, but many vendors offer bundled onboarding packages to streamline setup.
- Can endpoint management solutions handle BYOD devices? Yes, modern solutions support Bring Your Own Device (BYOD) environments through containerization, conditional access policies, and privacy-aware configurations. These features allow IT teams to secure corporate data without intruding on personal apps or content, ensuring compliance while respecting user boundaries.
Conclusion
Effective endpoint management is a strategic advantage that companies of all sizes should leverage over competitors. By streamlining device oversight, organizations can reduce operational burdens, enhance compliance, and support cost-efficient technology investments. The ability to monitor, secure, and optimize every endpoint empowers IT teams to proactively address challenges, rather than reactively troubleshooting issues as they arise.
Leveraging robust endpoint management tools helps ensure compliance with complex regulatory standards while maintaining visibility into device health and performance. The right solution not only protects sensitive data but also provides the metrics and transparency needed to communicate value to executive leadership. Features like BYOD support and lifecycle management further position businesses for resilience and adaptability in a cloud-first environment.
For organizations seeking to maximize their technology investments and maintain a secure, compliant posture, prioritizing endpoint management is essential. Start by assessing your current readiness and comparing available solutions to find the best fit for your needs. With the right strategy in place, your team will be well-equipped to support business growth and innovation without compromising on security or efficiency. Explore how our endpoint systems can support even the most complex endpoint environments.
Explore more on: